If you were not living under a rock for past sometime, you must have heard about the leaked NSA tools and the vulnerabilities getting exploited into the wild by WannaCry Ransomeware. This would be one of the most disastrous cyber-attack, once infected the ransomware encrypts user-files and asks for payment in Bitcoin to release decryption keys needed to unlock the files. As of today 298,455 machines are traced to be infected by this malware in over 150+ countries world-over. The first-line of defence to make sure your computer is not infected is to install latest Microsoft Updates and follow the advisory provided here, if you are late and infected WanaKiwi may be of help.

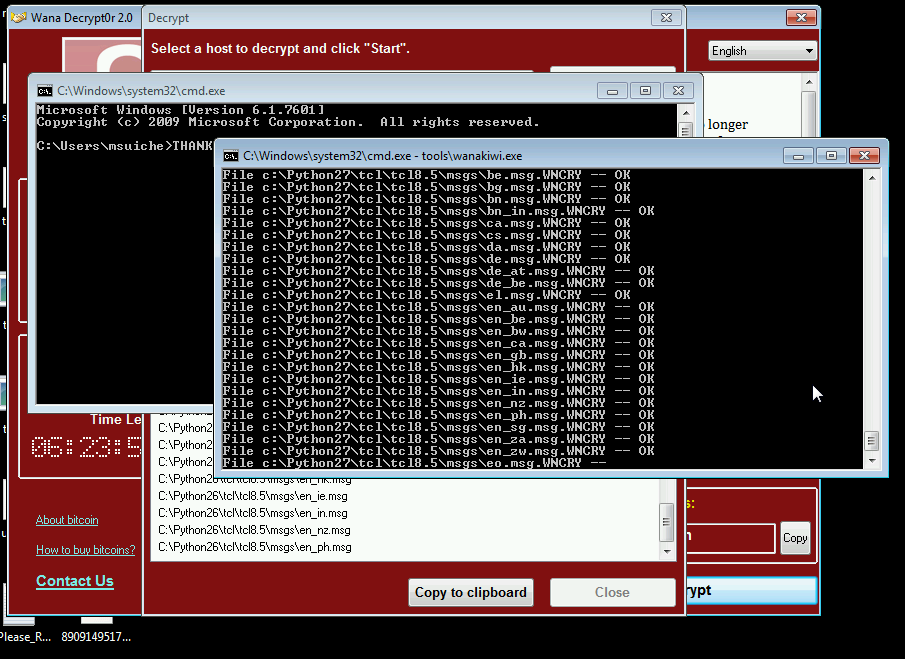
WanaKiwi, allows machines infected by the WannaCry ransomware to recover decryption keys. If you are LUCKY enough and the decryption keys are still in computer memory, this tool will recover the private user key in memory and dump it as 00000000.dky using which it will decrypt all encypted files without the need to pay ransom.
Do Note:
Given the fact this method relies on scanning the address space of the process that generated those keys, this means that if this process had been killed by, for instance, a reboot - the original process memory will be lost. It is very important for users to NOT reboot their system before trying this tool.
Secondly, because of the same reason we do not know how long the prime numbers will be kept in the address space before being reused by the process. This is why it is important to try this utility ASAP.
This is not a perfect tool, but this has been so far the best solution for victims who had no backup.
Usage and download instructions : https://github.com/gentilkiwi/wanakiwi
Standalone OFFLINE MS17-010 Patch Links For Microsoft Windows:
- Windows XP
- Windows Vista 32-bit
- Windows Vista 64-bit
- Windows 7 32-bit
- Windows 7 64-bit
- Windows 8 32-bit
- Windows 8 64-bit
- Windows 8.1 32-bit
- Windows 8.1 64-bit
- Windows 10 32-bit
- Windows 10 64-bit
- Windows 10 Version 1511 32-bit
- Windows 10 Version 1511 64-bit
- Windows 10 Version 1607 32-bit
- Windows 10 Version 1607 64-bit
Comments
WIFI HACKER
The world we live now is a complete package of technology and its successor, the Internet. Emerge of the internet have brought the whole world under one’s eye.
Add new comment